In a recent study, it turns out attackers can take control of electric cars using Bluetooth Low Energy (BLE). The technique allows attackers to hack into the electric system of Tesla cars or any other Bluetooth devices.
While the hack has only been demonstrated on electric cars, the researchers say that it could also be used on cars with other types of electronic systems, like those that use keyless entry. The Bluetooth relay system uses the phone key of Tesla cars to hack into the security system.
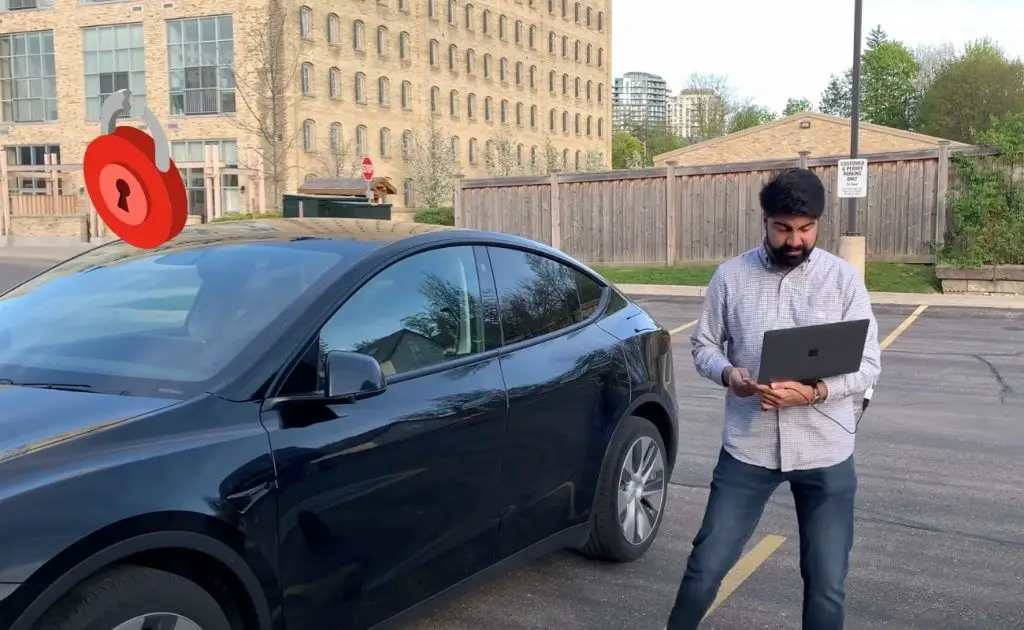
As car manufacturers increasingly rely on electronic systems to control vehicles, it’s crucial to be aware of the potential Bluetooth attacks in the future. However, the hack revealed by Sultan Qasim Khan from a security firm NCC group, is demonstrated using Tesla’s Model Y electric car.
Table of Contents
What Is Relay Station Attack?
Relay Station Attack of RSA is similar to a man-in-the-middle or MITM attack that uses the victim to position himself, letting the hacker eavesdrop on the existing data transfer or conversation.
The RSA or relay station attack works on the same method using the Bluetooth rays to access the secured network. Two attackers position themselves accordingly to get secured access to the Tesla car.
“Hacking into a car from hundreds of miles away tangibly demonstrates how our connected world opens us up to threats from the other side of the country—and sometimes even the other side of the world,” said Sultan Qasim Khan.
In 2015, a group of hackers demonstrated how they could take control of a Jeep Cherokee by hacking into the systems through the car’s Bluetooth connection. Those hackers were researching the Bluetooth hacking technique and were successful in implementing it. Jeep had to recall over a million cars after the zero-day exploit technique.
The researchers were able to remotely access the car’s steering, brakes, and other systems, raising serious questions about the safety of connected cars. While the Jeep hack was somewhat unusual in its methods, it’s not the first time that hackers have taken control of a car remotely.
As cars become increasingly connected and automated, they are also becoming more vulnerable to cyber-attacks. A recent study calls out the ease of hacking into any security system using Bluetooth signals.
How Does The Hack Work?
Khan explains the hack using two attackers, Attacker 1 and Attacker 2 to hack the locking system on a Tesla Model Y for the demonstration. Attacker 1 is standing near the Tesla’s location while Attacker 2 is in close proximity to the car’s owner.
The proximity matters as the first attacker are out of the range of the owner’s authenticating phone. Whereas the second one has a direct internet connection with Attacker 1 and is right in the proximity of the authenticating phone.
Attacker 1 sends authenticating signal to Tesla Model Y impersonating the owner’s credentials using Bluetooth enables the device. Attacker 1 transfers the Tesla Model Y authentication request received in response from the car to the Attacker 2. The owner’s phone responds to the authentication request received on Attacker 2’s device. Attacker 2 captures the automatic authentic credential response and relays the message to Attacker 1 promptly.
Khan demonstrates the attack using a simple diagram. The process consists of a very simple series of actions and can unlock any Tesla car using this attack technique.
How To Make Bluetooth Unlocking Safer?
The good news is that there are steps that drivers can take to protect themselves. For safety, it is crucial to ensure that the car’s Bluetooth connection is not visible to all searching devices.
It is crucial to avoid connecting to any unfamiliar Bluetooth devices and keep the system software up-to-date. Tesla owners should not only rely on Tesla phone authentication but use additional safety measures like a pin or disabling passive Bluetooth unlock functionality.
NCC Group study suggests automaker companies encourage developers to work on more stringent encryption modules for electric cars. Moreover, the study also calls out for educating end-users about the risk of such relay attacks on their electric cars.
“This research circumvents typical countermeasures against remote adversarial vehicle unlocking and changes the way we need to think about the security of Bluetooth Low Energy communications,” says Khan. By taking these precautions, you can help to keep your car safe from Bluetooth hacking.
What To Expect In The Future?
Hackers have already shown that they can exploit these vulnerabilities to take over the control of Bluetooth-enabled cars remotely. This research, conducted by specialists at the NCC Group, demonstrated how a hacker could gain control of a Tesla using a relay attack.
As we move towards a future of autonomous cars, it’s critical that we find ways to secure authentication data and vehicles against cyber threats. Bluetooth low energy link-layer induced relay-attack on various devices is becoming widespread.
One of the main concerns is that hackers are able to target Tesla cars remotely, without any need for physical access. This means that even stationed Tesla cars, even in secure locations are at risk. The study is enough to open the eyes of big auto giants like Tesla to understand the vulnerability of their cars getting hijacked.
It would be interesting to see what Tesla is going to say in response to this new study by the NCC Group. The future is challenging for electric car’s performance as well as their security. Comment down below to share your views on the possible threat to Tesla and other Bluetooth devices.



















Nope they can’t drive it away as Tesla has the pin to drive feature which will not work without the pin.
They may be able to replicate the Bluetooth signals but can not put the pin.
PIN number prevents drive away